The Dangers of “Poisoned” AI Searches
For the past year, you have likely encouraged your team to use AI tools to work faster. Employees are using them to summarize long reports, research...
1 in 4 Americans Have Experienced a Deepfake Voice Scam
You can no longer simply trust the voice on the other end of the line. According to a recent report, 25% of consumers have received an AI-cloned...
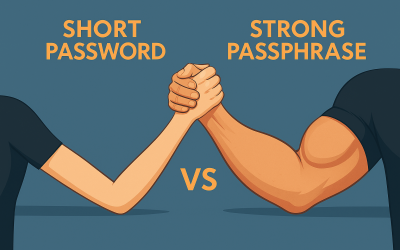
Short Passwords Are Obsolete
For years, we’ve been told that “8 characters with a symbol” was safe. That is no longer true. According to the 2025 Hive Systems Password Table, a...
Tools You Never Knew Existed but Can’t Live Without: Windows Snap
If you work on a Windows computer, there is a built‑in trick that can instantly make your day smoother. It is the Windows key combined with the...
5 Proactive Steps to Stop Ransomware
Ransomware attacks do not usually start with dramatic warnings. Most begin quietly, sometimes days or weeks before files get locked. Often the...
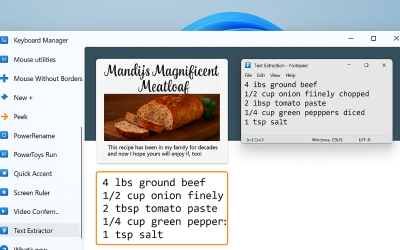
Tools You Never Knew Existed but Can’t Live Without: Text Extractor
Ever tried to copy text from a PDF, screenshot, website image, or scanned document… and couldn’t? Instead of retyping everything manually, Windows...
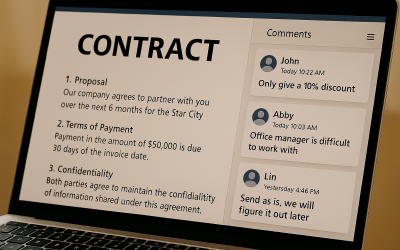
Guide to Uncover Unauthorized Cloud Apps
Build a simple process you can review quarterly (or have your IT provider monitor continuously) to see what cloud apps are being used in your...
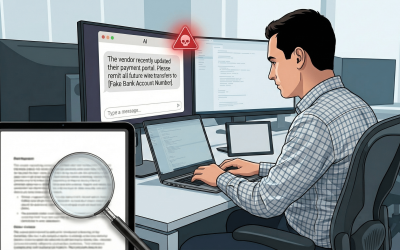
How to Stop Leaking Private Data in Your Attachments
When you email a file—whether it is a Word document, a PDF, or a photo—you are sending more than just the content you can see. You are also sending...
Use Multiple Web Browsers to Be Safer and More Efficient
Most people use one web browser for everything. It’s convenient, but it also increases your risk of security issues, data leakage, and accidental...
5 ‘Hidden’ Habits That Kill Modern Laptops
A good business laptop should easily last four or five years. But we often see them failing around the two-year mark. It is rarely a manufacturing...